ESET Endpoint Security for Windows
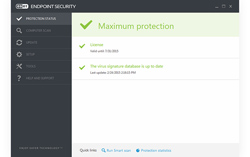
Comprehensive antimalware, with web filter, firewall and Botnet protection

Sorry, this product is no longer available, please contact us for a replacement.
For more pricing options, click here!
Overview:
ESET Endpoint Security delivers comprehensive IT security for your business via multiple layers of protection, including our field-proven ESET NOD32 detection technology, complete data access protection and fully adjustable scanning and update options. Keep your system running at its best thanks to low system demands, virtualization support and optional cloud-powered scanning. And oversee it all effortlessly with our completely redesigned, user-friendly remote administrator tool.
 Comprehensive antimalware, with web filter, firewall, and USB drive and botnet protection
Comprehensive antimalware, with web filter, firewall, and USB drive and botnet protection
- Comprehensive Endpoint Protection for Windows
- Virtualization Support + New Technology.Supports VMs and provides protection from hackers and botnets.
- Built-In Data Access Control. With Web Control to limit website access, and Two-Way Firewall.
- Low System Demands. Leaves more system resources free while still delivering complete protection.
- Remote Management. Fully manageable via the new ESET Remote Administrator web-console.
Benefits:
Endpoint Protection
- Antivirus and Antispyware
Eliminates all types of threats, including viruses, rootkits, worms and spyware.
Optional cloud-powered scanning: Whitelisting of safe files based on file reputation database in the cloud for better detection and faster scanning.
Only information about executable and archive files is sent to the cloud – such data are not personally attributable. - Virtualization Support
ESET Shared Local Cache stores metadata about already scanned files within the virtual environment so same files are not scanned again resulting in boosted scan speed.
ESET module updates and virus signatures database are stored outside of the default location, thus these don't have to be downloaded every time after the virtual machine is reverted to default snapshot. - Host-Based Intrusion Prevention System (HIPS)
Enables you to define rules for system registry, processes, applications and files.
Provides tampering protection and detects threats based on system behavior. - Exploit Blocker
Strengthens security of applications on users' systems, such as web browsers, PDF readers, email client or MS office components, which are commonly exploited.
Monitors process behaviors and looks for suspicious activities typical of exploits.
Strengthens protection against targeted attacks and previously unknown exploits, i.e. zero-day attacks. - Advanced Memory Scanner
Monitors the behavior of malicious processes and scans them once they decloak in the memory. This allows for effective infection prevention even from heavily obfuscated malware. - Client Antispam
Effectively filters out spam and scans all incoming emails for malware. Native support for Microsoft Outlook (POP3, IMAP, MAPI). - Cross-Platform Protection
ESET security solutions for Windows are capable of detecting Mac OS threats and vice-versa, delivering better protection in multi-platform environments.
Data Access Protection
- Web Control
Limits website access by category, e.g. gaming, social networking, shopping and others.
Enables you to create rules for user groups to comply with your company policies.
Soft blocking – notifies the end user that the website is blocked giving him an option to access the website, with activity logged. - Anti-Phishing
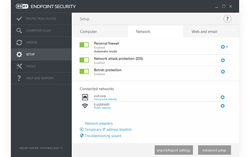
Protects end users from attempts by fake websites masquerading as trustworthy ones to acquire sensitive information such as usernames, passwords or banking and credit card details. - Two-Way Firewall
Prevents unauthorized access to your company network.
Provides anti-hacker protection and data exposure prevention.
Lets you define trusted networks, making all other connections, such as to public Wi-Fi, in ‘strict’ mode by default.
Troubleshooting wizard guides you through a set of questions, identifying problematic rules, or allowing you to create new ones. - Vulnerability Shield
Improves detection of Common Vulnerabilities and Exposures (CVEs) on widely used protocols such as SMB, RPC and RDP.
Protects against vulnerabilities for which a patch has not yet been released or deployed. - Botnet Protection
Protects against infiltration by botnet malware – preventing spam and network attacks launched from the endpoint. - Device Control
Blocks unauthorized devices (CDs/DVDs and USBs) from your system.
Enables you to create rules for user groups to comply with your company policies.
Soft blocking – notifies the end user that his device is blocked and gives him the option to access the device, with activity logged.
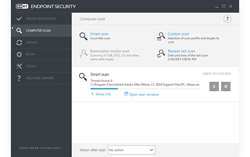
Scanning and Update Options
- Idle-State Scanner
Aids system performance by performing full scan proactively when the computer is not in use.
Helps speed up subsequent scans by populating the local cache. - First Scan after Installation
Provides the option to automatically run low priority on-demand scan 20 minutes after installation, assuring protection from the outset. - Update Rollback
Lets you revert to a previous version of protection modules and virus signature database.
Allows you to freeze updates as desired – opt for temporary rollback or delay until manually changed. - Postponed Updates
Provides the option to download from three specialized update servers: pre-release (beta users), regular release (recommended for non-critical systems) and postponed release (recommended for company-critical systems – approximately 12 hours after regular release). - Local Update Server
Saves company bandwidth by downloading updates only once, to a local mirror server.
Mobile workforce updates directly from ESET Update Server when the local mirror is not available. Secured (HTTPS) communication channel is supported.
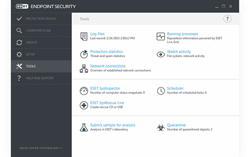
Usability
- RIP & Replace
Other security software is detected and uninstalled during installation of ESET Endpoint solutions. Supports both 32 and 64-bit systems. - Customizable GUI Visibility
Visibility of Graphical User Interface (GUI) to end user can be set to: Full, Minimal, Manual or Silent. Presence of ESET solution can be made completely invisible to end user, including no tray icon or notification windows.
By hiding the GUI completely, the “egui.exe” process does not run at all, resulting in even lower system resource consumption by the ESET solution. - ESET License Administrator
Makes it possible to handle all licenses transparently, from one place via web browser. You can merge, delegate and manage all licenses centrally in real-time, even if you are not using ESET Remote Administrator. - Touchscreen Support
Supports touch screens and high-resolution displays.
More padding for and complete rearrangement of GUI elements.
Basic frequently used actions accessible from tray menu. - Low System Demands
Delivers proven protection while leaving more system resources for programs that end users regularly run.
Can be deployed on older machines without the need for an upgrade, thereby extending hardware lifetime.
Conserves battery life for laptops that are away from the office, using battery mode. - Right-to-Left Language Support
Native right-to-left language support (e.g. for Arabic) for optimum usability. - Remote Management
ESET Endpoint solutions are fully manageable via ESET Remote Administrator.
Deploy, run tasks, set up policies, collect logs, and get notifications and an overall security overview of your network – all via a single web-based management console.
System Requirements:
Operating Systems:
- Microsoft Windows 10
- Microsoft Windows 8.1
- Microsoft Windows 8
- Microsoft Windows 7
- Microsoft Windows Vista
- Microsoft Windows XP
Compatible with ESET Remote Administrator 6
- Note: Not compatible with previous versions of ESET Remote Administrator
- See more information about ESET Remote Administrator compatibility
Product Comparison:
| ESET Endpoint Antivirus | ESET Endpoint Security | |
| Endpoint Security for Windows Comparison | ||
|---|---|---|
| Platform | Windows | Windows |
| Antivirus and Antispyware Comes with built-in data access protection and protects against all types of threats, including viruses, rootkits, worms and spyware. |
||
| Virtualization Support Designed for virtual environments with a range of features for seamless operation and high performance. |
||
| Anti-Phishing Protects end users from fake websites trying to acquire sensitive information, such as usernames, passwords, banking credit card details. |
||
| Web Control Limits user access to select websites or website categories, e.g. gaming, social networking, shopping. |
– | |
| Two-Way Firewall Prevents unauthorized access to company network and provides effective anti-hacker protection and data exposure prevention. |
– | |
| Botnet Protection Protects against infiltration by botnet malware – preventing spam and network attacks launched from the endpoint machine. |
– | |
| Antispam Effectively filters out spam on user's endpoint device and scans all incoming emails for malware. |
– | |
| Remote Management Fully manageable via ESET Remote Administrator. |
||
Documentation:
Download the ESET Endpoint Security for Windows Datasheet (PDF).
Pricing Notes:
- Antivirus, firewall and antispam for business use 5+ licenses. It protects workstations, and has Remote Administrator (RA) for centralized management. Media: License Download.
- Pricing and product availability subject to change without notice.